Terraform Providers: Complete Configuration and Management Guide
Learn about what Terraform providers are and how to use them with examples.
TL;DR
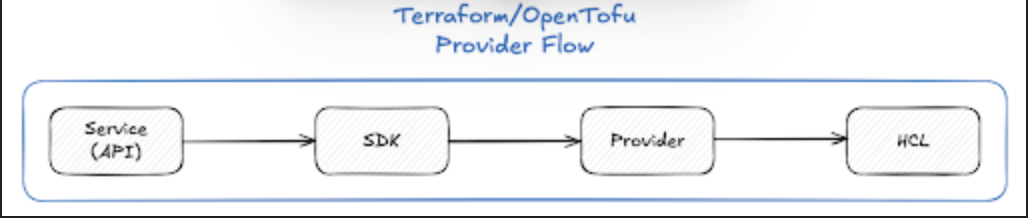
- A Terraform (or OpenTofu) provider is the plugin that translates your HCL into API calls — AWS, Azure, GCP, Kubernetes, Datadog, Okta, and hundreds more.
- Configuring a provider is two steps: declare it in
required_providerswith a version constraint, then configure auth/region/etc. in aproviderblock. - Pin versions with
~>(allow patch updates) for stability; never leave a provider unconstrained. - Commit
.terraform.lock.hclto git and pre-populate hashes for every platform your team or CI runs on — this is the supply-chain security layer most teams skip. - Never hardcode credentials. Use environment variables locally, IAM roles / managed identities on cloud, and OIDC in CI/CD.
- Use provider aliases for multi-region and multi-account work; pass them explicitly via the
providersargument when calling modules.
Terraform providers are the backbone of infrastructure as code, acting as the critical connection between your HCL configuration files and the APIs of cloud platforms, SaaS services, and other infrastructure systems. Understanding how to configure, manage, and version providers effectively is fundamental to building scalable, secure, and reproducible infrastructure.
This pillar article provides a complete guide to Terraform provider management, covering everything from basic configuration to advanced patterns and best practices for enterprise environments. Whether you're on Terraform or the open-source OpenTofu fork, the configuration model is identical — both use the same provider plugin protocol.
What Are Terraform Providers?
A Terraform provider is a plugin that enables Terraform to interact with specific cloud providers (AWS, Azure, Google Cloud), SaaS platforms, APIs, or any external service with a REST or gRPC interface. The provider configuration tells Terraform how to authenticate and connect to these services.
Without a properly configured provider, Terraform has no way of managing your resources. Each provider plugin adds a set of resource types and data sources that your infrastructure code can then manage.
Core Provider Responsibilities
Providers handle:
- Authentication: Managing credentials, tokens, and API keys
- API Communication: Making calls to cloud provider APIs
- Resource Management: Creating, updating, and destroying infrastructure objects
- Data Source Queries: Retrieving information about existing infrastructure
- Service-Specific Features: Handling region/location selection, custom endpoints, and other platform-specific settings
Provider Blocks and Configuration
Configuring providers in Terraform involves two essential steps: declaring the required providers and then configuring them.
Step 1: Declare Required Providers
Provider requirements are defined in the required_providers block within the top-level terraform block. This tells Terraform where to find each provider and which versions are acceptable.
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 5.0"
}
azurerm = {
source = "hashicorp/azurerm"
version = ">= 3.0.0, < 4.0.0"
}
google = {
source = "hashicorp/google"
version = "~> 5.0"
}
}
}Each provider entry specifies:
- Local name (e.g.,
aws): How you reference the provider in your configuration - Source: The full address of the provider (format:
[hostname/]namespace/type) - Version constraint: Which versions are compatible with your configuration
Step 2: Configure the Provider
After declaring requirements, configure providers with provider blocks. This is where you specify authentication details and default settings.
# Default AWS provider
provider "aws" {
region = "us-east-1"
# Authentication typically handled via environment variables or IAM roles
}
# Azure provider
provider "azurerm" {
features {}
}
# Google Cloud provider
provider "google" {
project = "my-gcp-project"
region = "us-central1"
}Authentication Best Practices
Never hardcode credentials in your configuration files. Instead:
- Use Environment Variables: Set
AWS_ACCESS_KEY_ID,AWS_SECRET_ACCESS_KEY, etc. before running Terraform - Leverage IAM Roles: In AWS environments, use instance profiles or EKS service accounts
- Use Service Accounts: In GCP and Azure, use service account keys or managed identities
- Implement OIDC: For CI/CD pipelines, use OpenID Connect for short-lived, credential-free authentication
- Secrets Management: Integrate with HashiCorp Vault, AWS Secrets Manager, or Azure Key Vault
Provider Aliases for Multi-Region and Multi-Account Deployments
For scenarios requiring multiple configurations of the same provider, use provider aliases. This is essential for:
- Deploying resources across multiple AWS regions
- Managing resources in different AWS accounts
- Using different API endpoints or authentication methods
- Creating resources in multiple cloud providers simultaneously
Defining Provider Aliases
# Default provider for us-east-1
provider "aws" {
region = "us-east-1"
}
# Aliased provider for us-west-2
provider "aws" {
alias = "west"
region = "us-west-2"
}
# Aliased provider for eu-west-1
provider "aws" {
alias = "europe"
region = "eu-west-1"
}Using Aliases in Resources
Resources use the default provider unless explicitly specified:
# Uses default us-east-1 provider
resource "aws_instance" "app_east" {
ami = "ami-0c55b31ad20f0c502"
instance_type = "t3.micro"
tags = {
Name = "app-east"
}
}
# Uses west alias (us-west-2)
resource "aws_instance" "app_west" {
provider = aws.west
ami = "ami-068f09e03c69f0b76"
instance_type = "t3.micro"
tags = {
Name = "app-west"
}
}
# Uses europe alias (eu-west-1)
resource "aws_vpc" "europe_vpc" {
provider = aws.europe
cidr_block = "10.0.0.0/16"
tags = {
Name = "europe-vpc"
}
}Passing Aliases to Modules
When using modules that require specific provider configurations, pass them via the providers argument:
module "vpc_east" {
source = "./modules/vpc"
# Uses default provider
}
module "vpc_west" {
source = "./modules/vpc"
providers = {
aws = aws.west
}
cidr_block = "10.1.0.0/16"
}The child module must declare the provider in its required_providers block.
Provider Requirements and Version Constraints
Provider requirements form the foundation of reproducible infrastructure deployments. They ensure that specific provider versions are downloaded and used consistently across all environments.
Version Constraint Operators
Terraform supports several operators for expressing version constraints:
| Operator | Description | Example | Effect |
|---|---|---|---|
= |
Exact version | = 5.0.0 |
Only version 5.0.0 |
!= |
Exclude version | != 5.0.1 |
Any version except 5.0.1 |
> |
Greater than | > 5.0.0 |
Version 5.0.1 and newer |
>= |
Greater or equal | >= 5.0.0 |
Version 5.0.0 and newer |
< |
Less than | < 6.0.0 |
Versions before 6.0.0 |
<= |
Less or equal | <= 5.10.0 |
Version 5.10.0 and earlier |
~> |
Pessimistic constraint | ~> 5.0.0 |
Only rightmost version component increments |
Pessimistic Constraint Operator
The ~> operator is particularly useful as it balances stability with automatic updates:
~> 5.0allows any version in the 5.x series (5.0.0, 5.1.0, 5.9.9)~> 5.0.0allows only patch updates (5.0.0, 5.0.1, 5.0.99)~> 5.1.0allows patch updates starting from 5.1.0
Combining Constraints
Create complex version ranges by combining constraints with commas:
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 5.0, != 5.5.0" # Allow 5.x except 5.5.0
}
azurerm = {
source = "hashicorp/azurerm"
version = ">= 3.50.0, < 4.0.0" # Range constraint
}
}
}Versioning Strategy by Use Case
Pinned versions (critical environments): Use exact versions
version = "5.67.1" # Exact version requiredReusable modules (libraries): Use looser constraints for compatibility
version = ">= 5.0.0" # Specify minimum version onlyRoot modules (applications): Use tight constraints for stability
version = "~> 5.67.0" # Allow patch updates onlyDependency Lock Files (.terraform.lock.hcl)
The .terraform.lock.hcl file is Terraform's critical security and consistency mechanism. Introduced in Terraform 0.14, it records the exact provider versions and cryptographic checksums used in your configuration.
Why Lock Files Matter
Without lock files, terraform init would select the latest provider version matching your constraints each time it runs. This creates the "works on my machine" problem where different environments use different provider versions, leading to inconsistent behavior.
Lock files solve three critical challenges:
- Reproducibility: Ensures identical provider versions across all deployments
- Supply Chain Security: Verifies provider package integrity through cryptographic checksums
- Cross-Platform Consistency: Enables smooth collaboration across Linux, macOS, and Windows systems
Lock File Structure
A .terraform.lock.hcl file has this structure:
# This file is maintained automatically by "terraform init".
# Manual edits may be lost in future updates.
provider "registry.terraform.io/hashicorp/aws" {
version = "5.38.0"
constraints = "~> 5.0"
hashes = [
"h1:A2B3C4D5E6F7G8H9I0J1K2L3M4N5O6P7Q8R9S0T1U2V3W4X5Y6Z7A8B9C0D1E2F3",
"zh:0573de96ba316d808be9f8d6fc8e8e68e0e6b614ed4d8d11eed83062c9b60714",
"zh:37560469042f5f43fdb961eb6c6b7f6e0bccec04c1c7cbf90f5d6d97893e6c3d",
# Additional platform-specific hashes...
]
}
provider "registry.terraform.io/hashicorp/azurerm" {
version = "3.85.0"
constraints = ">= 3.0, < 4.0"
hashes = [
# Hashes for this provider...
]
}Each provider block contains:
- version: The exact provider version selected
- constraints: The version constraints from your configuration
- hashes: Cryptographic checksums for provider packages on different platforms
When Lock Files Are Created and Updated
- Initial creation: When running
terraform initfor the first time - During updates: When running
terraform init -upgradeorterraform initwith new providers - Platform additions: When Terraform installs a provider on a new OS/architecture combination
Lock files are NOT updated during terraform plan, terraform apply, or terraform destroy operations.
Platform-Specific Hash Management
Lock files created on one platform (e.g., macOS) only contain checksums for that architecture. To support multi-platform teams, pre-populate checksums:
terraform providers lock \
-platform=linux_amd64 \
-platform=darwin_amd64 \
-platform=darwin_arm64 \
-platform=windows_amd64This ensures your lock file works across all team members' development machines and CI/CD pipelines.
Lock File Best Practices
- Always commit to version control: Never add
.terraform.lock.hclto.gitignore - Review lock file changes: Treat lock file updates like code changes in pull requests
- Use intentional upgrades: Only run
terraform init -upgradewhen you explicitly want to update providers - Pre-populate for multiple platforms: Especially critical for teams with mixed OS environments
- Separate lock files per configuration: Each independent Terraform configuration has its own lock file
Lock File Debugging and Troubleshooting
Lock file issues are common, especially in multi-platform and team environments. Understanding how to diagnose and resolve them is essential.
Checksum Mismatch Errors
The most common error:
ERROR: Failed to install provider
Error while installing hashicorp/null v3.2.4: the current package for
registry.terraform.io/hashicorp/null 3.2.4 doesn't match any of the
checksums previously recorded in the dependency lock file.
Causes:
- Lock file created on one platform (macOS) used on another (Linux CI/CD)
- Provider version constraints updated without updating the lock file
- Corrupted local plugin cache
- Provider binary tampering (security risk)
Solutions:
Delete and reinitialize (last resort):
rm .terraform.lock.hcl
terraform initUpgrade providers intentionally:
terraform init -upgradeThen commit the updated lock file.
Add checksums for all platforms (most common fix):
terraform providers lock \
-platform=linux_amd64 \
-platform=darwin_amd64Stale Lock Files
Problem: Version constraints updated but lock file not refreshed
Solution:
terraform init -upgrade
git add .terraform.lock.hcl
git commit -m "Update provider versions"Merge Conflicts in Lock Files
Problem: Multiple developers update different providers simultaneously
Solution: After resolving the merge conflict, run terraform init to validate all entries:
# Manually resolve conflict in .terraform.lock.hcl
terraform init
git add .terraform.lock.hcl
git commit -m "Resolve lock file merge conflict"Provider Authentication Patterns
Different providers and environments require different authentication approaches.
Environment Variables
The simplest method for development:
# AWS
export AWS_ACCESS_KEY_ID="your-key"
export AWS_SECRET_ACCESS_KEY="your-secret"
# Azure
export ARM_CLIENT_ID="your-client-id"
export ARM_CLIENT_SECRET="your-secret"
export ARM_TENANT_ID="your-tenant-id"
# GCP
export GOOGLE_CREDENTIALS='{"type": "service_account", ...}'Cloud-Native Authentication
AWS IAM Roles (recommended for EC2, ECS, Lambda):
provider "aws" {
region = "us-east-1"
# Automatically uses EC2 instance role credentials
}Azure Managed Identities:
provider "azurerm" {
features {}
# Automatically uses managed identity credentials
}GCP Service Accounts:
provider "google" {
project = "my-project"
# Automatically uses default application credentials
}OIDC for CI/CD Pipelines
The most secure approach for automated deployments. (Note: Terraform Cloud's free tier was discontinued on March 31, 2026 — Scalr and Spacelift offer the same OIDC flow.)
terraform {
cloud {
organization = "my-org"
hostname = "app.terraform.io"
}
}
provider "aws" {
region = "us-east-1"
# Terraform Cloud handles OIDC token exchange for short-lived credentials
}Secrets Management Integration
For sensitive credentials, integrate with dedicated systems:
provider "aws" {
region = "us-east-1"
assume_role {
role_arn = "arn:aws:iam::123456789012:role/terraform-role"
}
}Popular Terraform Providers Overview
AWS (Amazon Web Services)
The most widely used provider for cloud infrastructure.
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 5.0"
}
}
}
provider "aws" {
region = "us-east-1"
}
resource "aws_vpc" "main" {
cidr_block = "10.0.0.0/16"
tags = {
Name = "main-vpc"
}
}
resource "aws_subnet" "main" {
vpc_id = aws_vpc.main.id
cidr_block = "10.0.1.0/24"
availability_zone = "us-east-1a"
}See detailed guides: Top 10 Most Popular Terraform Providers and AWS Provider v6.0: What's Breaking in April 2025
Azure (Microsoft Azure)
For managing resources in Microsoft's cloud platform.
terraform {
required_providers {
azurerm = {
source = "hashicorp/azurerm"
version = "~> 3.0"
}
}
}
provider "azurerm" {
features {}
}
resource "azurerm_resource_group" "main" {
name = "example-resources"
location = "East US"
}
resource "azurerm_storage_account" "main" {
name = "examplestg"
resource_group_name = azurerm_resource_group.main.name
location = azurerm_resource_group.main.location
account_tier = "Standard"
account_replication_type = "LRS"
}Google Cloud (GCP)
For Google Cloud Platform infrastructure.
terraform {
required_providers {
google = {
source = "hashicorp/google"
version = "~> 5.0"
}
}
}
provider "google" {
project = "my-gcp-project"
region = "us-central1"
}
resource "google_storage_bucket" "main" {
name = "my-unique-bucket-name"
location = "US"
force_destroy = false
}
resource "google_compute_instance" "main" {
name = "web-server"
machine_type = "e2-micro"
zone = "us-central1-a"
}Kubernetes
For managing Kubernetes clusters and resources.
terraform {
required_providers {
kubernetes = {
source = "hashicorp/kubernetes"
version = "~> 2.0"
}
}
}
provider "kubernetes" {
config_path = "~/.kube/config"
config_context = "my-cluster"
}
resource "kubernetes_namespace" "example" {
metadata {
name = "example-namespace"
}
}
resource "kubernetes_deployment" "example" {
metadata {
name = "example-deployment"
namespace = kubernetes_namespace.example.metadata[0].name
}
spec {
replicas = 3
# ... deployment specification
}
}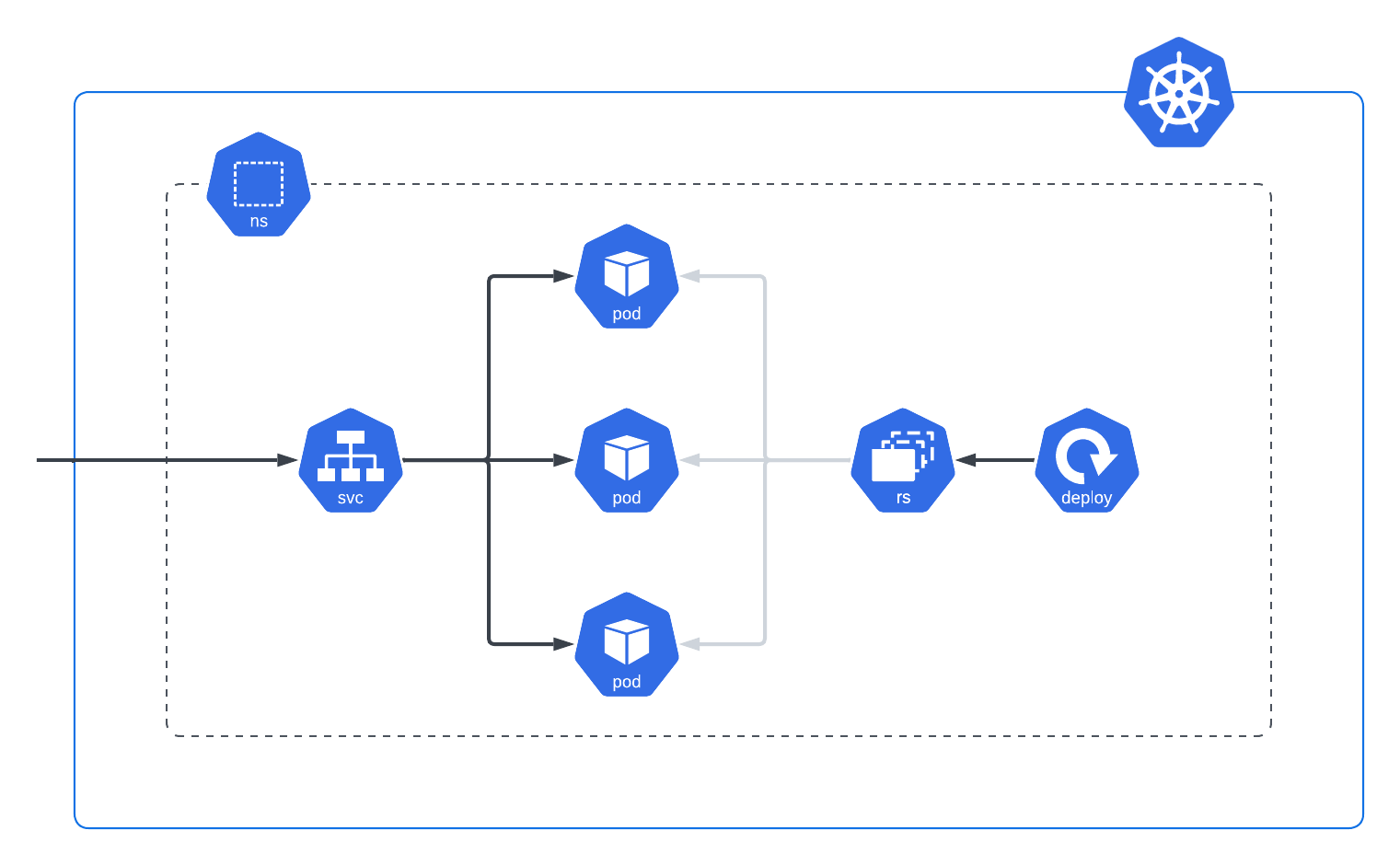
See detailed guide: Mastering Kubernetes with Terraform: A Provider Deep Dive
Datadog
For monitoring and observability infrastructure.
terraform {
required_providers {
datadog = {
source = "DataDog/datadog"
version = "~> 3.0"
}
}
}
provider "datadog" {
api_key = var.datadog_api_key
app_key = var.datadog_app_key
api_url = "https://api.datadoghq.com/"
}
resource "datadog_monitor" "cpu_alert" {
type = "metric alert"
query = "avg(last_5m):avg:system.cpu.user{*} > 0.9"
message = "CPU utilization is high"
}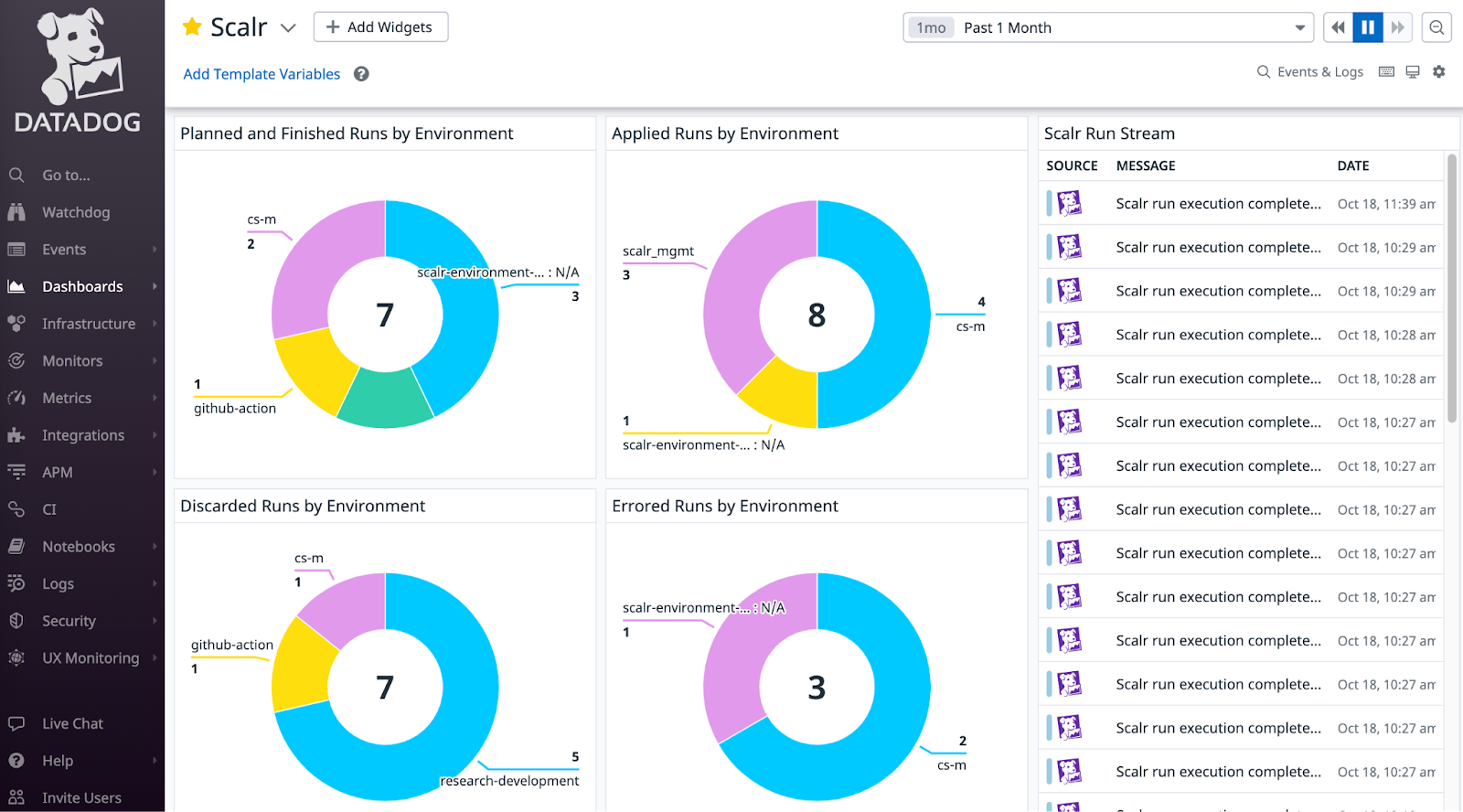
See detailed guide: How to Use the Datadog Terraform Provider
Okta
For identity and access management.
terraform {
required_providers {
okta = {
source = "okta/okta"
version = "~> 4.0"
}
}
}
provider "okta" {
org_name = var.okta_org_name
base_url = "okta.com"
api_token = var.okta_api_token
}
resource "okta_user" "example" {
first_name = "John"
last_name = "Doe"
login = "[email protected]"
email = "[email protected]"
}See detailed guide: How to Use the Terraform Okta Provider
Best Practices for Terraform Providers in 2026
1. Version Management and Lock Files
- Always use explicit version constraints: Never leave providers unconstrained
- Commit lock files to version control: These should never be ignored
- Pre-populate multi-platform checksums: Essential for diverse teams
- Document provider updates: Include context in commit messages and pull requests
- Automate provider updates: Use scheduled pipelines to test and merge minor/patch version updates
2. Credential and Authentication Security
- Never hardcode credentials: This is non-negotiable
- Use OIDC for CI/CD: Eliminate static credentials in automation
- Implement least privilege: Grant only necessary IAM permissions
- Rotate credentials regularly: Especially for long-lived API keys
- Separate credentials per environment: Use different accounts for dev/staging/prod
- Audit credential usage: Monitor provider authentication and API calls
3. Multi-Provider and Multi-Account Strategies
- Use aliases strategically: Only when managing distinct configurations of the same provider
- Separate configurations by environment: Use directory structure (environments/dev, environments/prod) rather than workspaces
- Leverage IaC platforms for credential management: Tools like Scalr centralize provider credentials and enforce policies
- Document provider architecture: Maintain clear diagrams showing which providers manage which infrastructure
4. Module Design with Providers
- Declare required providers in all modules: Even if inheriting from parent
- Pass aliases explicitly to modules: Use the providers map in module blocks
- Use provider defaults judiciously: Only for the primary use case
- Version external modules carefully: Test provider version compatibility before upgrades
5. Environment Management
- Separate lock files per environment: Don't share lock files across dev/staging/prod
- Use environment-specific .tfvars: Parameterize provider configurations
- Implement automated testing: Validate provider configurations in pipelines
- Plan for disaster recovery: Ensure provider credentials are secured and backed up
6. Operational Excellence
- Monitor provider API usage: Track rate limiting and quota consumption
- Document custom provider configurations: Especially for complex alias setups
- Standardize on approved providers: Avoid provider proliferation through governance
- Regular provider audits: Review which providers are in use and if all are actively managed
- Test provider migrations: Plan upgrades carefully, especially major versions
7. Enterprise Considerations
- Centralize provider credential management: Use IaC platforms rather than distributed .env files
- Enforce provider version policies: Use policy-as-code (OPA) to prevent breaking changes
- Implement approval workflows: For sensitive provider configurations or multi-account access
- Maintain provider registries: Consider private registries for internal or vetted providers
- Cross-team coordination: Document provider ownership and support contacts
Common Provider Configuration Pitfalls
Unconstrained Provider Versions
Problem: Provider blocks without version constraints allow unexpected major version upgrades
# BAD: No version constraint
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
# Missing version!
}
}
}Solution: Always specify meaningful version constraints
# GOOD: Explicit version constraint
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 5.0" # Allow patch updates only
}
}
}Hardcoded Credentials
Problem: Credentials visible in source code and version control
# BAD: Never do this
provider "aws" {
access_key = "AKIAIOSFODNN7EXAMPLE"
secret_key = "wJalrXUtnFEMI/K7MDENG/bPxRfiCYEXAMPLEKEY"
region = "us-east-1"
}Solution: Use environment variables or cloud-native authentication
# GOOD: Credentials from environment
provider "aws" {
region = "us-east-1"
# Uses AWS_ACCESS_KEY_ID and AWS_SECRET_ACCESS_KEY environment variables
}
# BETTER: Use IAM roles or OIDC
provider "aws" {
region = "us-east-1"
# Automatically uses IAM role credentials
}Missing Lock Files in Version Control
Problem: Lock file ignored or not committed, leading to inconsistent provider versions
Solution:
# Remove from .gitignore if present
git rm --cached .terraform.lock.hcl
# Commit the lock file
git add .terraform.lock.hcl
git commit -m "Add Terraform provider lock file"Inconsistent Provider Configurations Across Modules
Problem: Root module configures providers but modules redefine them differently
Solution: Configure providers only in root modules, have modules declare requirements without configuration
# In root module
provider "aws" {
region = "us-east-1"
}
# In child module
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 5.0"
}
}
}
# No provider block here - inherits from rootConclusion
Terraform providers are fundamental to infrastructure as code. Mastering their configuration, management, and versioning practices is essential for building stable, secure, and reproducible infrastructure at scale.
The key to successful provider management is:
- Be intentional about version constraints and updates
- Prioritize security in credential handling
- Maintain consistency through lock files and clear documentation
- Automate where possible to reduce manual errors
- Plan for scale with multi-account and multi-environment strategies
As infrastructure continues to grow in complexity, proper provider management becomes increasingly critical. Whether managing a single provider or orchestrating deployments across multiple clouds and accounts, the practices outlined in this guide will serve as a solid foundation for your infrastructure as code journey.
For enterprise organizations managing Terraform at scale, consider IaC management platforms like Scalr that centralize provider credential management, enforce policies, and provide visibility into how providers are configured and used across your entire infrastructure portfolio.
This blog has been verified for Terraform and OpenTofu
