Maintaining Terraform Module Health with Dependabot and Scalr
Maintaining Terraform Module Health with Dependabot and Scalr
Terraform modules are the foundation for scalable deployments, but maintaining these building blocks requires platform teams to be stringent. In this blog, we are going to talk about different methods and tools to ensure you retain module health for all-sized infrastructure teams. The combination of the Scalr module registry, Dependabot, and pull request based deployments provide a path to ensuring secure and up to date modules for all of your deployments.
Components
Before we get into the solution, I want to cover a few other components that will be discussed in the remainder of the blog:
- Dependabot - Dependabot is GitHub's automated dependency update tool that scans repositories for outdated dependencies and automatically creates pull requests to update them. It helps development teams stay current with security patches and new version updates by monitoring package manifests and alerting teams when dependencies need attention.
- Scalr - Scalr is a Terraform automation and collaboration (TACO) platform that provides organizations with a centralized approach for managing Terraform. Platform teams can ensure they have control over the ecosystem while enabling self-service for development teams.
- Private Module Registry - A module registry allows organizations to publish approved and version-controlled modules for use by their development teams. This helps ensure the organization's security and coding standards are followed by all teams and it helps the developer experience as they are able to use the Terraform modules as building blocks rather than creating the Terraform code themselves.
What is Terraform Module Health and Why Does it Matter?
Terraform module health refers to the overall quality, maintainability, and reliability of your infrastructure-as-code components. Like any software asset, Terraform modules accumulate technical debt over time as dependencies age, security vulnerabilities emerge, and cloud provider services evolve. Maintaining healthy Terraform modules ensures your infrastructure remains secure, compliant, and optimized for current best practices. Module health directly impacts operational stability since outdated modules may introduce compatibility issues, performance bottlenecks, or security risks that can cascade throughout your infrastructure. Neglecting regular maintenance often leads to costly emergency remediations and unplanned outages, whereas proactive health monitoring enables development teams to schedule updates during maintenance windows. Organizations with mature DevOps practices typically implement automated scanning tools that continuously evaluate module health metrics, including dependency freshness, code quality, security posture, and cloud provider compatibility, allowing them to maintain infrastructure resilience as business requirements and technologies change.
Versioning Terraform modules in a private registry provides advantages for maintaining Terraform module health. A versioned private registry creates a controlled environment where teams can systematically manage Terraform module lifecycles, ensuring backward compatibility and providing clear upgrade paths for consumers. When Terraform modules are versioned in a central private registry, teams gain visibility into which infrastructure components are using outdated modules, allowing for prioritized maintenance efforts. The private registry becomes a single source of truth, eliminating confusion about which Terraform module version should be used for specific environments or projects. This centralization also facilitates automated testing of modules across different versions, enabling teams to verify that updates don't break existing infrastructure before releasing them. Ultimately, a versioned module registry transforms infrastructure management from an ad-hoc, reactive process into a predictable process.
How Does Scalr and Dependabot Help?
Scalr and Dependabot work together to create a method for maintaining Terraform module health through automation. This integration provides the following capabilities:
Scalr provides a private module registry where organizations can store and version their Terraform modules, while Dependabot automatically scans these modules for new versions. When updates are detected, Dependabot creates a pull request to update module references in your Terraform code, ensuring you're always using the latest version. This automation significantly reduces the manual effort required to maintain the Terraform configuration files.
Additionally, Scalr provides reporting capabilities that offer visibility into Terraform module usage across workspaces, enabling teams to identify which modules are being used where, ensure compliance with organizational standards, and measure the effectiveness of their module strategy. The reporting will help quickly identify workspaces that might not be using Dependabot, which will be evident by the Terraform module version being out of date.
Implementation
Before working through this, ensure you have an account in scalr.io and GitHub.
Step 1: Obtain a fine-grained Scalr API access token
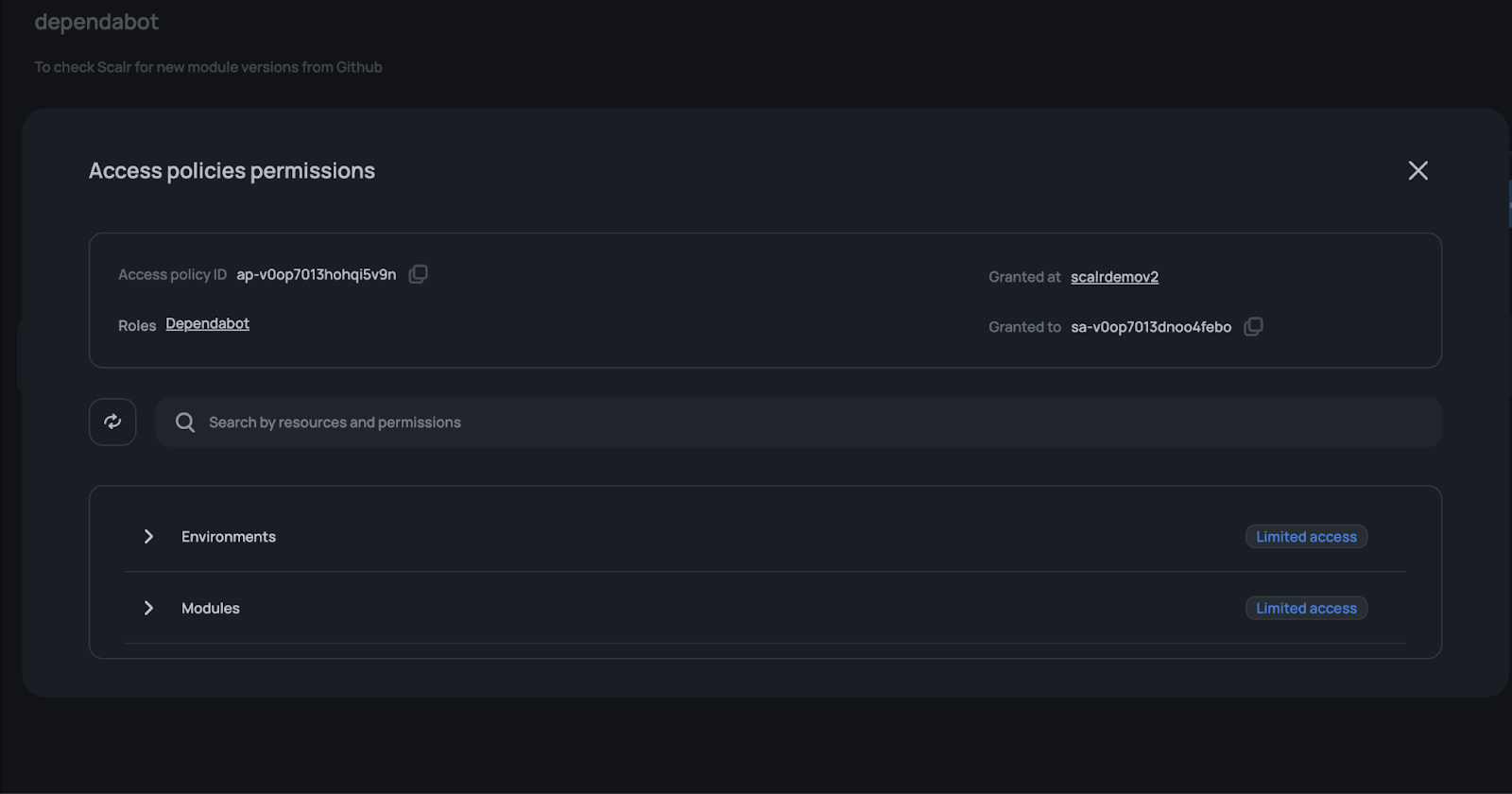
First, you need to create a custom role with minimal access to the Scalr API. To read all modules (both from the account and environment scopes), the API key has to be granted the following permissions:
- Go to Security > IAM > Roles.
- Click on the "New role"
- Enter a role name, e.g. Dependabot
- Click on the "Add permissions" and add the following permissions: environments:read and modules:read
Create a service account and assign the role from the previous step:
- Go to Security > IAM > Service Accounts.
- Click on the "New service account"
- Enter a name, e.g. dependabot
- Click on "Grant access", select the role selected in the previous step, and keep "Grant On" as "Account".
- Optionally, set owners of the service account. More about owners you can read here.
After a service account is created, generate the API access token by clicking on the Generate token.
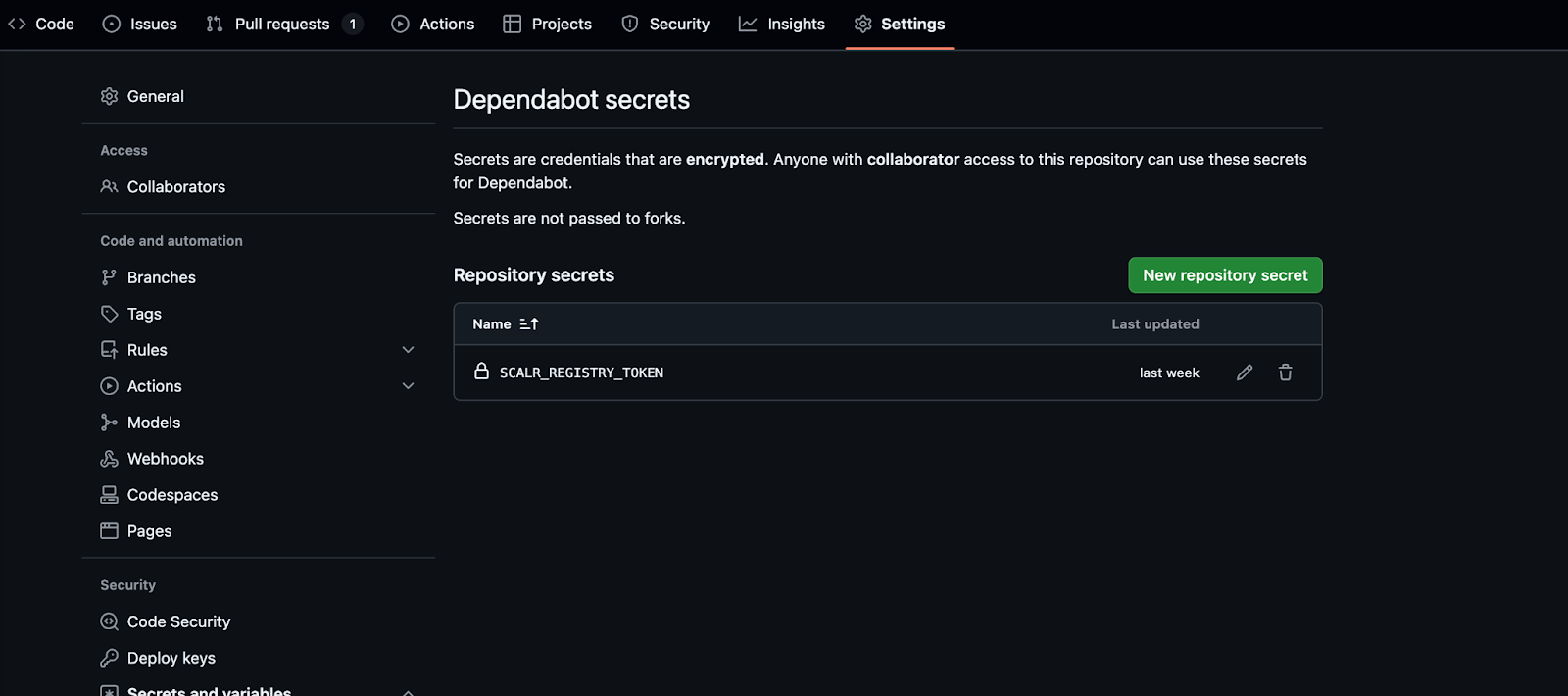
Step 2: Store the Scalr API Token in GitHub Secrets
- Navigate to your repository on GitHub.
- Go to Settings > Secrets and variables > Dependabot.
- Click New repository secret.
- Add the following secret: Name: SCALR_REGISTRY_TOKEN, Value: Your Scalr API token from the previous step.
- Save the secret.
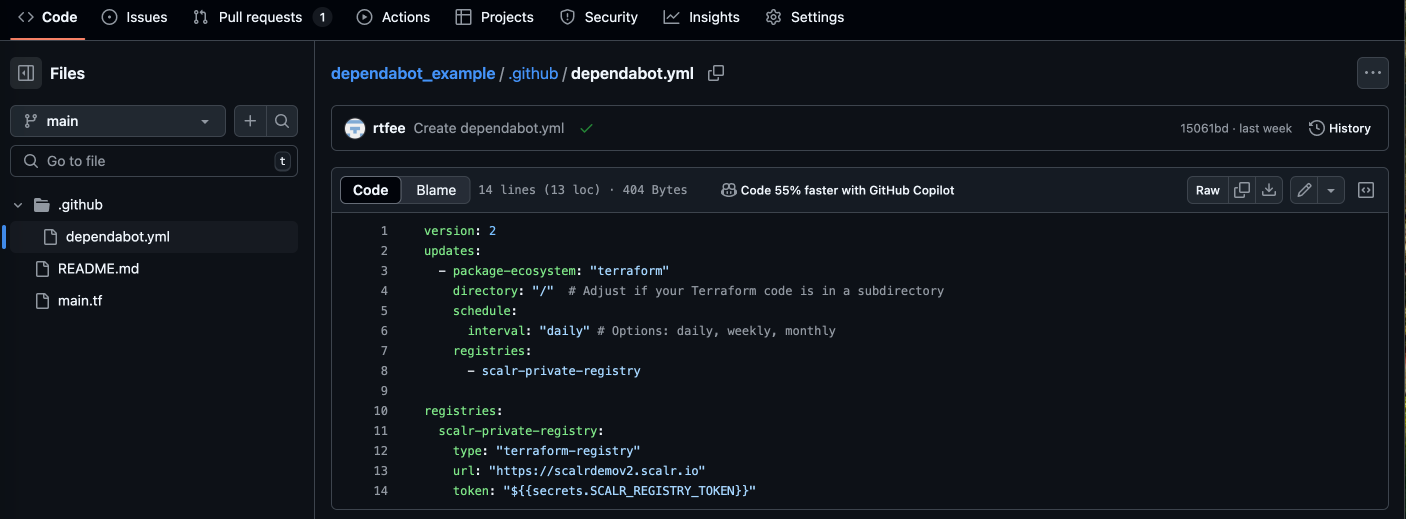
Step 3: Configure .github/dependabot.yml
Create or update the .github/dependabot.yml file in your repository with the following content:
version: 2
updates:
- package-ecosystem: "terraform"
directory: "/" # Adjust if your Terraform code is in a subdirectory
schedule:
interval: "weekly" # Options: daily, weekly, monthly
registries:
- scalr-private-registry
registries:
scalr-private-registry:
type: "terraform-registry"
url: "https://your-account.scalr.io"
token: "${{secrets.SCALR_REGISTRY_TOKEN}}"Further Information:
package-ecosystem: "terraform"instructs Dependabot to check Terraform dependencies.directory: "/"specifies where the Terraform code is located. Add multiple entries if needed for subdirectories.schedule.interval: "weekly"defines how often Dependabot checks for updates.- The registries section configures Dependabot to authenticate with Scalr using the API token.
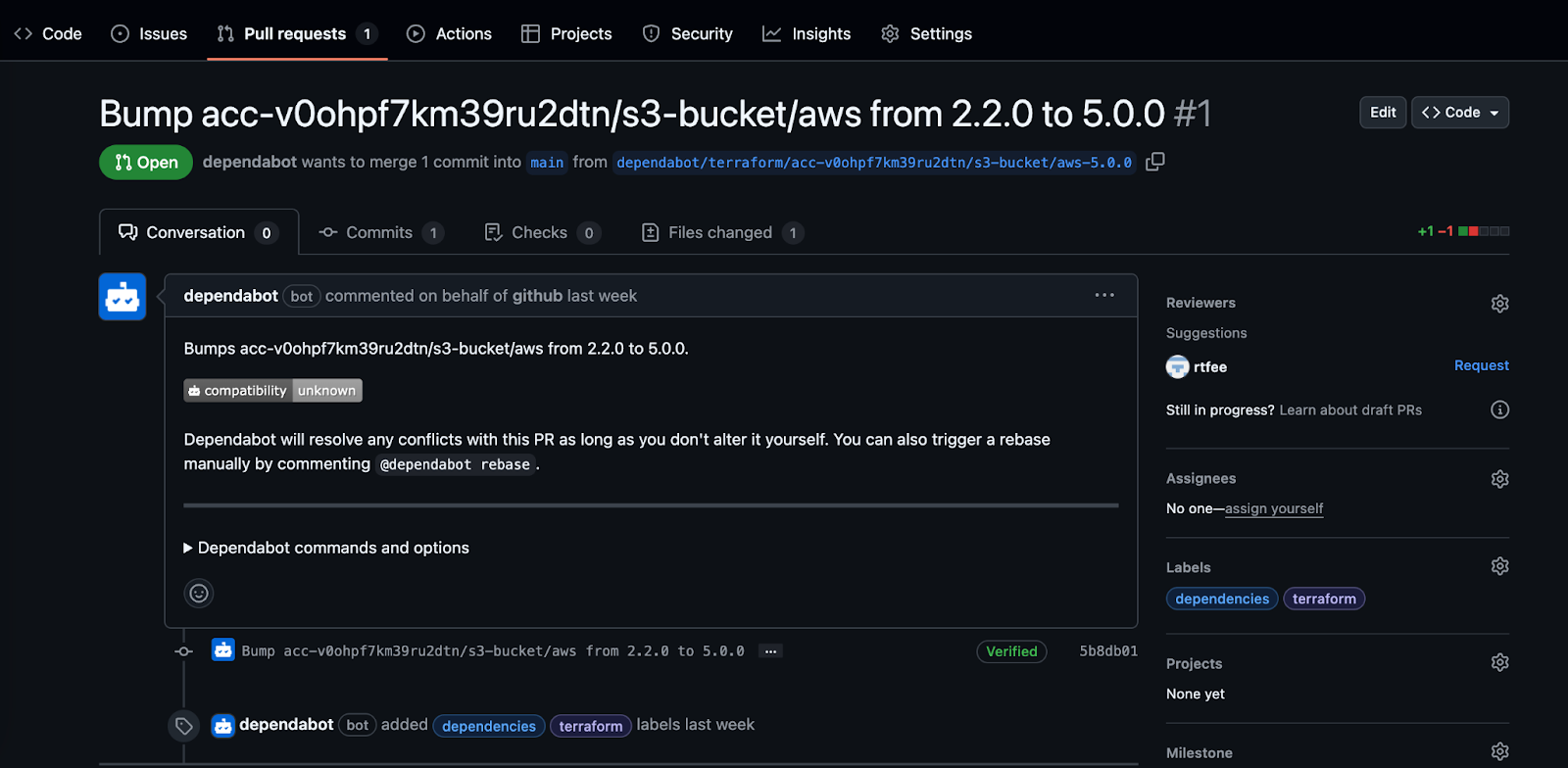
Step 4: Commit and Push Changes
- Add the .github/dependabot.yml file to your repository.
- Commit and push the changes.
- Navigate to Pull Requests > Dependabot in GitHub to verify that Dependabot is fetching updates.
The next time a new version is pushed, you will see that Dependabot will notice the change and automatically create the pull request:
Summary
Integrating Scalr's private module registry with Dependabot's automated scanning capabilities creates a system that continuously monitors your Terraform modules for outdated dependencies and security vulnerabilities. This creates a proactive maintenance workflow, where a new version is automatically identified and pull requests are generated with detailed change logs, eliminating the manual tracking of module versions across your infrastructure ecosystem. By implementing this automation, your developers know when to update their Terraform code rather than having the platform team chase them down, resulting in an improved experience for all teams.
