New Feature: Custom Hooks
The custom hooks feature makes it easy to customize your Terraform workflow while using Scalr as the remote backend.
We're happy to announce custom hooks that make it easier to customize your Terraform workflow while using Scalr as the remote backend.
Scalr makes it easier to automate and collaborate with your colleagues, but we recognize that different organizations and teams might have unique workflows, which is why we have now added the custom hooks feature within workspaces.
Problem
Normally, users are accustomed to running Terraform from their laptop or an environment where they have the freedom to have a completely custom runtime environment. When running Terraform in a remote backend, you are restricted to what is already installed in that environment … until now.
Solution
Custom hooks allow you to execute any command you would normally run in a Linux command line before and/or after the plan and before and/or after the apply. Common use cases are:
- Executing tools (tflint, checkov, etc) before a plan to run lint or security tests
- Pulling the plan JSON and uploading it to a third party system
- Install software needed as part of your Terraform run before the plan or apply
- Triggering API calls to a third party (Slack, Teams, etc) after the run has successfully completed.
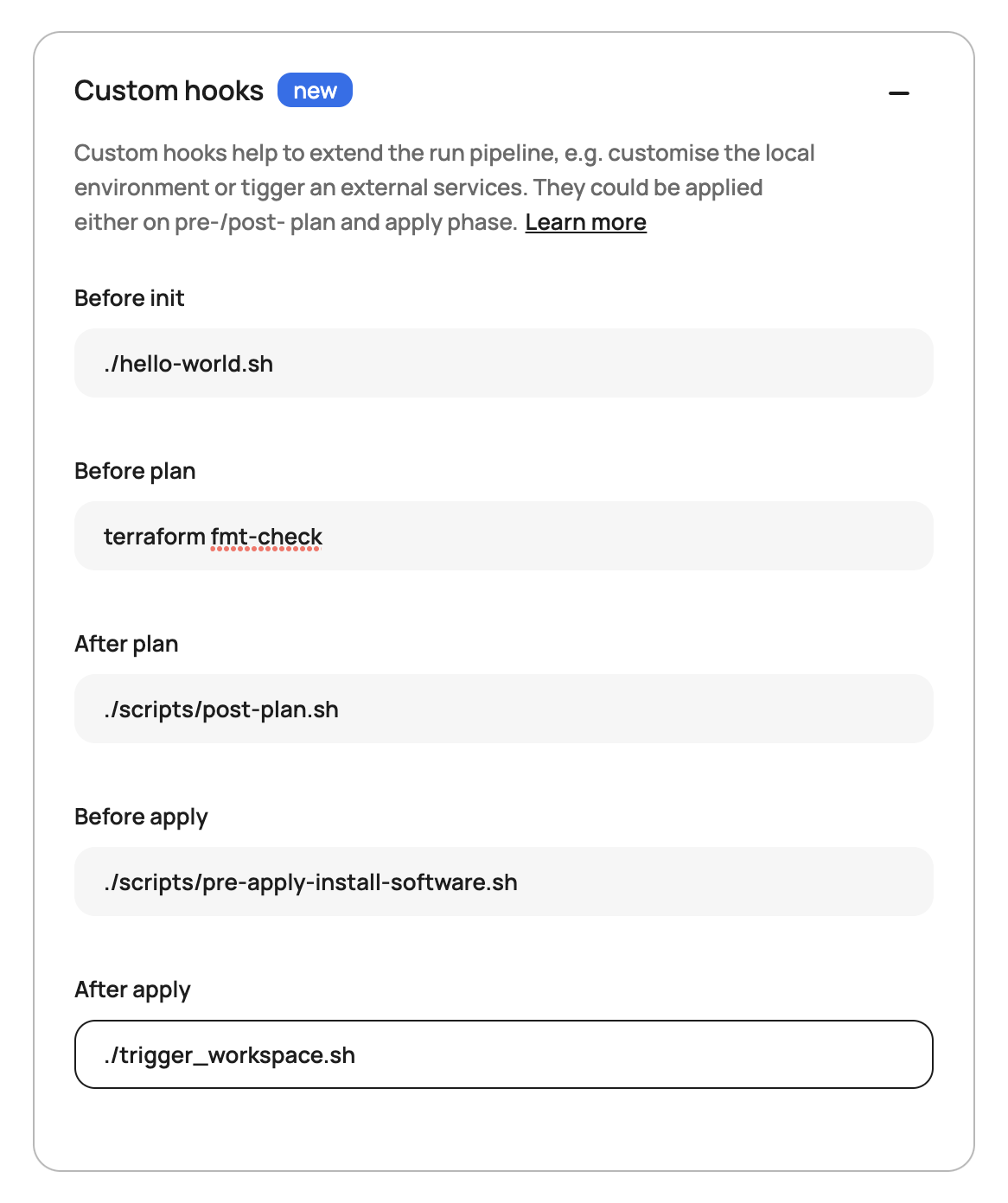
Here is what it looks like in the workspace settings:
How to Get Started
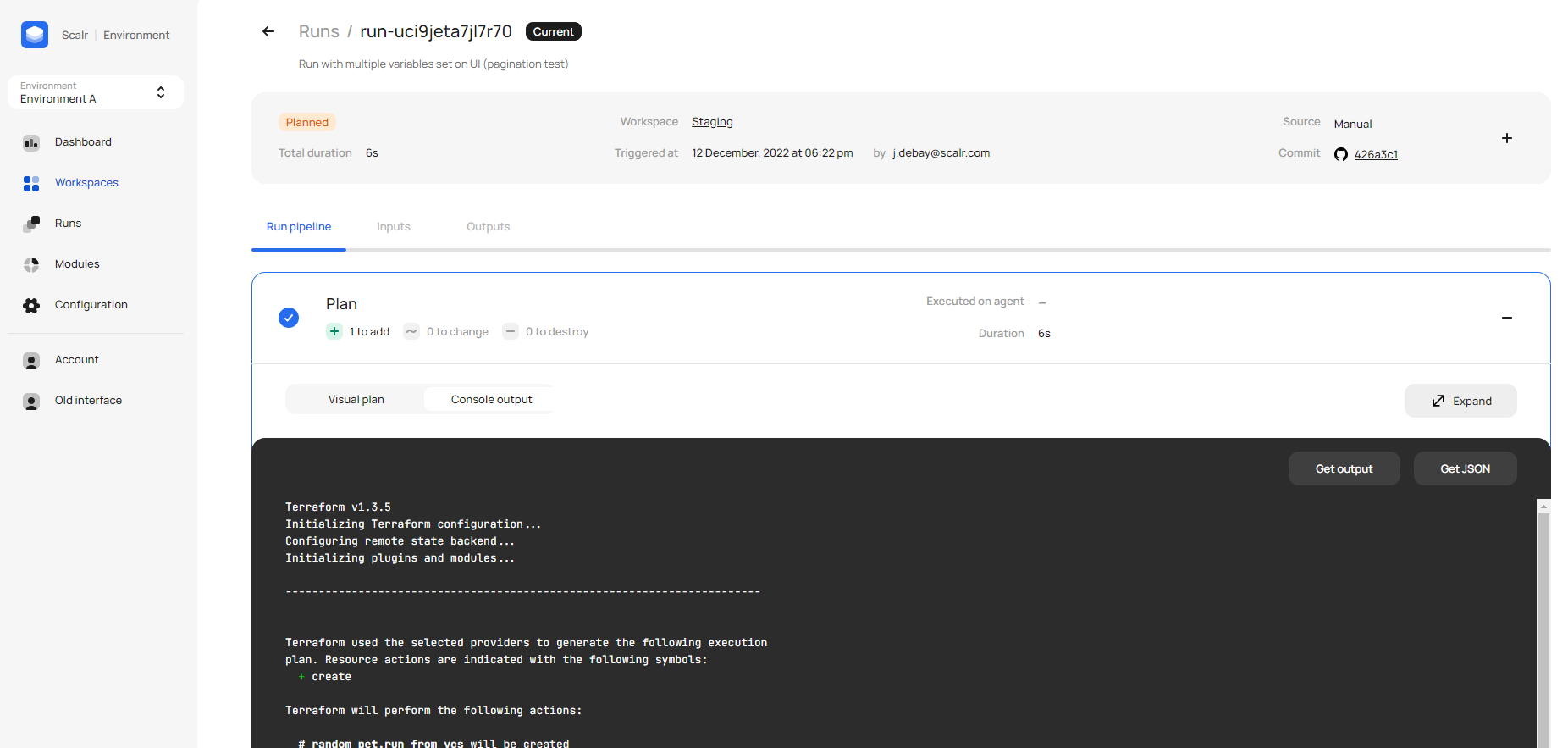
To try the hooks out, go to the settings of any one of your workspaces where you will find the custom hooks section. As seen in the screenshot above, just enter in your standard commands, which are passed to the runtime environment and executed as part of the run. The output can be found in the plan and apply output:
Built-in Variable: SCALR_RUN_IS_DESTROY
As of July 2023, Scalr added a new built-in variable that can be used with Custom Hooks: SCALR_RUN_IS_DESTROY. This variable allows you to incorporate logic into your custom hook scripts, enabling you to differentiate between Terraform apply and Terraform destroy operations.
How does it work? By analyzing the return code, you can determine the nature of the run:
- A return code of 1 means the run is a Terraform destroy.
- A return code of 0 indicates a Terraform apply.
This allows you to implement intelligent logic in your custom hook scripts, ensuring the right actions are triggered at the right time. For example, you might skip certain post-apply notifications when a destroy is running, or trigger a cleanup script only on destroy operations.
With Custom Hooks and SCALR_RUN_IS_DESTROY, you can automate pre- and post-run processes or customize actions based on specific environments and operation types, removing the need for manual adjustments.
Log in to try it out for yourself and check out more examples in the docs.
